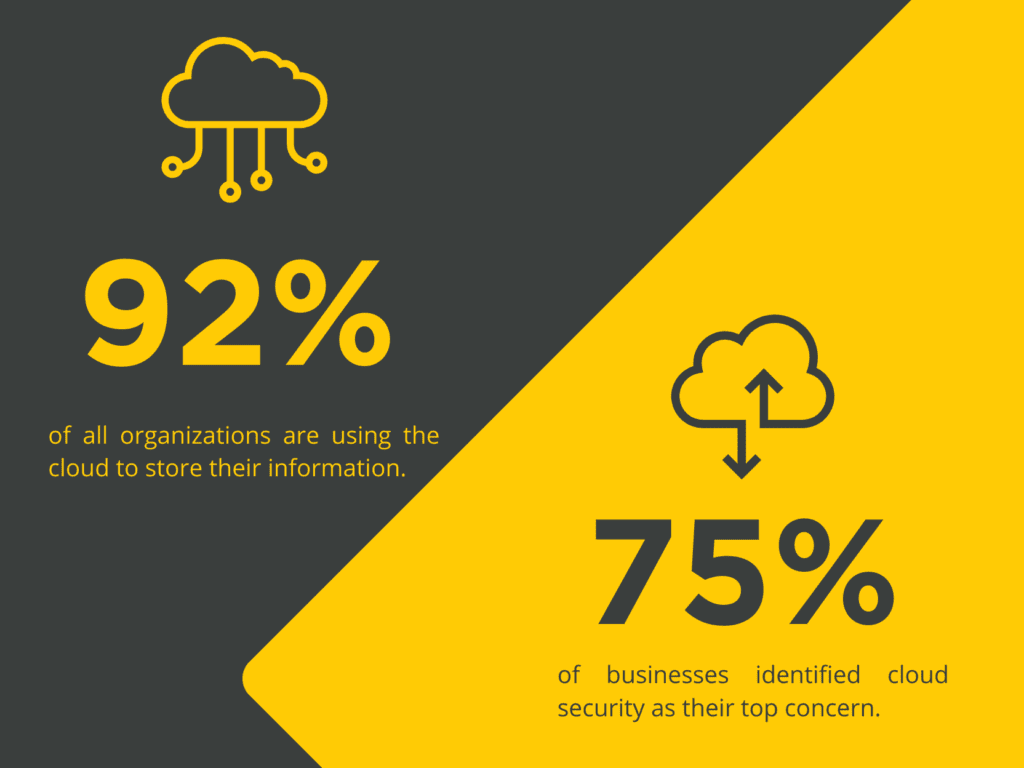
As businesses increasingly rely on cloud technology for data storage and application hosting, it is crucial to understand the importance of cloud security. With over 92% of all organizations using the cloud to store their information, the modern business landscape depends on the cloud to operate efficiently. In contrast, 75% of businesses identified cloud security as their top concern. This has exposed businesses to cyber threats and attacks that can severely damage their reputation and revenue.
This article will explore the significance of addressing cloud security threats and the critical challenges in cloud security.
The Importance of Cloud Security in Business
Safeguarding valuable corporate data is crucial for businesses, emphasizing the importance of cloud security. This protection extends to protecting intellectual property and ensuring compliance with data privacy regulations. Additionally, cloud security helps maintain regulatory compliance and protects sensitive information from various threats, including malicious insiders and natural disasters. Businesses must prioritize cloud security to mitigate potential risks associated with public internet.
The Increasing Reliance on Cloud Technology in Businesses
The escalating dependence on cloud technology in enterprises demands robust security measures to ensure data security and compliance. The imperative need for cloud security is underscored by the expanding use of cloud applications, emphasizing access management, and protecting sensitive data. With the surge in cloud deployments, businesses must prioritize security controls, accountability, and regulatory compliance to mitigate the impact of cloud adoption on data privacy. This growing reliance on cloud technology requires comprehensive security measures to safeguard against malicious insiders, and potential breaches.
The Significance of Addressing Cloud Security Threats in the Modern Business Landscape
Organizations must prioritize data security in the modern business landscape to mitigate cloud threats effectively. These threats include data loss, unauthorized access, and compliance issues. Understanding these threats is vital for safeguarding sensitive data and intellectual property. Effective measures are essential for maintaining regulatory compliance and protecting valuable corporate assets As cloud adoption continues to rise, businesses must address these threats proactively to ensure a secure environment for their data.
Key Challenges in Cloud Security
Cloud security presents several challenges such as ensuring compliance with regulatory requirements and access control management across cloud environments. Incident response within cloud computing and network security concerns in cloud deployments are also critical. Organizations must address these challenges to uphold data security, compliance, and privacy, ensuring a resilient defense against malicious insiders, natural disasters, and cyber-attacks.
Threats for Data Stored in the Cloud
The security of data stored in the cloud is susceptible to unauthorized access, posing a risk to sensitive information. Cloud storage security concerns include potential data breaches and loss incidents, necessitating cloud users to address security issues with service providers. Furthermore, phishing attacks and insider threats contribute to the vulnerability of valuable data stored in cloud environments. Human error also plays a significant role in cloud security risks, emphasizing the need for robust security measures.
Vulnerability of Applications on Cloud
Applications deployed on the cloud are susceptible to various security vulnerabilities. Weak passwords and access management issues can compromise the security of cloud applications, posing a risk to sensitive data. Additionally, denial of service attacks and data privacy risks are prevalent threats cloud applications face. Security controls in cloud deployments play a crucial role in addressing these vulnerabilities. Furthermore, corporate networks and cloud resources are impacted by cloud network security risks, highlighting the importance of robust security measures in cloud adoption.
Digital Skilling for Enhanced Cloud Security
Building a highly skilled workforce is crucial for mitigating cloud security risks in today’s dynamic digital landscape. Organizations can empower their employees to recognize and combat common cloud security threats by providing comprehensive training and education on cybersecurity best practices. Ongoing digital skilling initiatives ensure that cybersecurity and IT professionals stay updated with compliance requirements.
The Role of a Skilled Workforce in Mitigating Cloud Security Risks
In safeguarding against cloud security threats, a skilled workforce plays a pivotal role. Equipping employees with proper training enables them to identify and manage potential risks effectively. Ongoing education and awareness programs keep the workforce updated with the latest security trends and best practices. A well-trained workforce is better equipped to handle security incidents, thus minimizing their impact. Investing in digital skilling can be a critical differentiator for businesses seeking to enhance their cloud security posture.
Importance of Ongoing Training and Development Programs for Employees
In the realm of cybersecurity, workforce training holds immense importance. Our training programs at Elev8 are specifically designed to focus on your organization’s cybersecurity training needs. Employee training and development programs are crucial in enhancing data security within an organization. Companies can ensure regulatory requirements by keeping employees updated on the latest threats and security measures. Educating employees on identifying and responding to threat actors in the cloud environment is essential. These training programs should cover technical skills, good security practices, and ensure accountability in handling malicious insiders.
Specific Digital Skills Needed to Combat Cloud Security Threats
In combating cloud security threats, specific digital skills play a crucial role. Expertise in network security, and encryption technologies is essential for adequate cloud security. Furthermore, proficiency in risk management and compliance regulations is necessary to mitigate threats such as data breaches and hacking. Cloud security professionals must stay updated on the latest security threats and possess experience with security tools and software. Investing in staff training and hiring skilled professionals is vital to ensuring secure cloud computing.
Future Trends in Cloud Security
The landscape of cloud security is evolving rapidly, driven by emerging technologies and innovative approaches to data protection. Machine learning and artificial intelligence are increasingly utilized to identify and mitigate security threats. In contrast, the shift towards a zero-trust security model ensures that data access is restricted to only those with a genuine need. Blockchain technology is gaining traction for secure data transfer and storage, and the adoption of containerization and microservices architecture enhances security and scalability. Furthermore, ongoing emphasis on employee education remains critical in preventing human error and insider threats.
Emerging Technologies for Cloud Security
As cloud security continues evolving, emerging technologies play a crucial role in safeguarding sensitive data. Machine learning and artificial intelligence are now employed to identify and prevent potential breaches within cloud environments proactively. Blockchain technology offers secure access control and robust auditing mechanisms, while cloud providers are implementing hardware-based security measures to protect against physical attacks. Moreover, quantum computing-resistant encryption is developing to counter future threats. Furthermore, multi-factor authentication and biometric identification are increasingly enhancing the overall security posture of cloud environments.
How Can Businesses Stay Ahead of Upcoming Cloud Security Threats?
Conducting cloud security audits can help identify vulnerabilities. Training employees in solid password management and working with reputable cloud service providers can enhance cloud security. Implementing multi-factor authentication is also recommended. Cytek has partnered with organizations like yours to reduce cyber threats and ensure effective cloud security measures and compliance with regulations.
Contact our experts to discuss how your team can stay prepared to handle cloud security threats.




